Back to Blog
Secure-by-Design Perspectives
The Offensive AI Watershed and What It Means for Security Architecture

, Co-founder & CEO
The attackers already made the shift. Security architecture has to follow.
In February 2026, AWS published an incident report that every security leader should read.
A single actor, with low to medium technical skill, compromised over 600 FortiGate firewall devices across 55 countries in five weeks. No zero-days. No nation-state resources. No team.
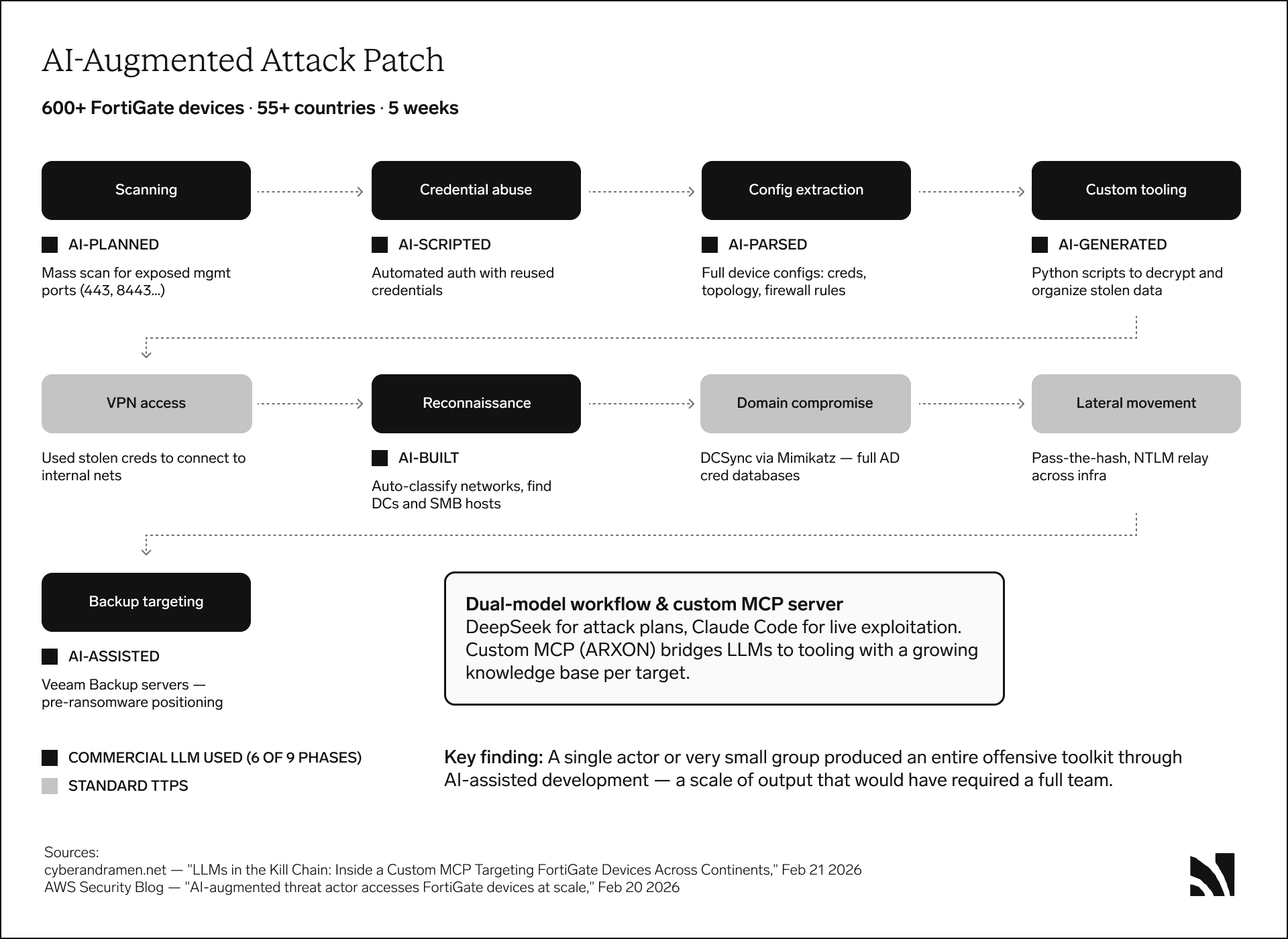
The actor scanned the internet for FortiGate management interfaces left exposed on standard ports. Found hundreds. Authenticated with default or weak credentials. Then used AI to do the rest.
DeepSeek generated attack plans from the reconnaissance data. Claude, configured as a coding agent, built the entire offensive toolkit: config parsers, credential extractors, VPN automation, scanning orchestration, results dashboards. A Model Context Protocol server maintained memory across all 600 targets, so every compromise made the next one faster. The code had all the hallmarks of AI output, but it worked. At a scale that would have required a full engineering team two years ago.
This isn't a cautionary tale about what could happen. It happened. Five weeks ago.
AI is changing the threat landscape in ways that detection and response can't absorb.
The FortiGate case is striking not because the technique was sophisticated, but because the scale was. One person. 600 targets. Five weeks. That ratio used to be impossible. It isn't anymore.
AI has fundamentally changed three things about the threat landscape. The pool of capable attackers is now much larger, because skill is no longer the constraint it was. The speed of attacks has collapsed. CrowdStrike measured average breakout time, from initial access to lateral movement, at 29 minutes in 2025, with the fastest documented case at 27 seconds. And the scale at which any single actor can operate has expanded by orders of magnitude, scanning thousands of organizations simultaneously, building purpose-built tooling for each, maintaining institutional memory across every target.
The numbers reflect this. CrowdStrike recorded an 89% year-over-year increase in AI-enabled adversary operations in 2025. Google's Threat Intelligence Group identified over 57 nation-state groups actively using commercial AI for offensive operations. Anthropic documented the first fully autonomous AI-orchestrated espionage campaign in late 2025, with AI handling 80 to 90 percent of the operation with minimal human intervention. And the FortiGate case wasn't a nation-state. It was one person.
The consequence for how we think about security strategy is significant. Detection and response was built for a threat environment where attacks took time: time to develop, time to execute, time to move laterally. That time created the window defenders needed to find and contain the threat. AI is closing that window faster than detection-based security can adapt. At 29 minutes average breakout time, by the time an alert fires, gets triaged, and reaches a human, the attacker is already deep inside the environment.
Faster detection helps at the margin. But it doesn't change the underlying dynamic. If the conditions that enable the attack exist, AI-powered attackers will find them and exploit them before the response can catch up. The only durable answer is to eliminate the conditions in the first place.
The organizations that weren't in the report had one thing in common.
There's one detail in the AWS report worth pausing on. When the actor encountered hardened targets, closed ports, enforced controls, properly scoped access, they moved on. They didn't try harder. They went to the next target. The architecture itself turned away the attack. No alert, no incident, no entry in the report.
We've always known that getting the fundamentals right matters. What's changed is the consequence of not doing it. With AI on the other side systematically scanning every organization, every account, every exposed endpoint at once, failing to get the architecture right is no longer a question of if you'll be found. It's when. And by the time it happens, it's already too late.
The answer is architecture. The challenge is closing the gap between intent and reality.
Every security leader knows what good looks like. Least-privilege access. Controls enforced at the organization level. Security designed into provisioning, not patched in after the fact. The principles aren't new.
The difficulty is operationalizing them at cloud scale. A single enterprise might have hundreds of AWS accounts, multiple Azure subscriptions, active workloads on GCP, and an OCI tenancy for a specific application. Translating security intent, what you want to be true, into enforceable architecture across all of it, kept current as the environment changes, and validated before deployment so it doesn't break production, is genuinely hard. Most organizations end up with partial coverage, and the gaps accumulate faster than teams can close them.
That gap is what AI-powered attackers are built to find. The answer isn't better detection of what's already wrong. It's architecture that enforces security natively, through the cloud provider's own controls, so the conditions attackers are scanning for don't exist in the first place.
Security leaders are already recognizing the shift.
The market data reflects it. Cloud security is the fastest-growing segment in security spending, projected at 25.9% CAGR through 2028. Investment is following the problem, and the problem is increasingly in the cloud, where environments move fast and the gap between security intent and security reality tends to be widest.
The strategic direction is also shifting. Gartner forecasts that by 2030, preemptive cybersecurity solutions will account for 50 percent of IT security spending, up from less than 5 percent today. The reasoning is straightforward: a security strategy centered on detection and response was designed for a slower threat. It needs to be rebuilt for this one.
More budget moving toward prevention. More investment in controls that stop the attack before it starts. The industry is catching up to what the threat environment already demands.
Closing the gap.
We build the control plane that translates security intent into enforceable architecture across AWS, Azure, GCP, and OCI, at the speed the cloud actually operates. So that when an attacker brings AI speed and scale to bear, what they find is an environment that doesn't give them anywhere to go.
If this is a problem you're working on, we'd love to talk.

About Amit Megiddo
Amit Megiddo is the CEO and Co-founder of Native. He previously led product management for Amazon GuardDuty from its inception, growing it into one of the world’s most widely adopted cloud security services. Building on his AWS experience and earlier leadership roles, Amit drives Native with the same customer obsession, believing success comes from delivering the best possible product.
Continue reading

Security Architecture & Strategy
May 18, 2026
Detection sits downstream of the change. The remediation loop is human-paced. The cloud architecture still allows it. Four structural reasons CSPM cannot stop recurrence, and the enforcement layer that does.

Security Architecture & Strategy
May 15, 2026
The work of seeing and detecting is mature. The next chapter is enforcement, architecture, and secure-by-design. Native is now in AWS Security Hub Extended with multicloud coverage across AWS, Azure, GCP, and OCI.



